Infosec Security Policy Template
Infosec Security Policy Template - Developing a robust information security policy template requires careful attention to several key components. Bcategories, and applicable sans policy templates. Establish clear responsibilities for everyone involved in managing and protecting information, from the. For a cyber security policy to be truly effective, it should cover the following essential areas: Key elements of a cyber security policy. Our experienced professionals will help you to customize these free it security policy template options and make them correct for your specific business needs. These are free to use and fully customizable to your company's it security practices. An access control policy defines how your organization manages user access to systems, data, and applications. Iso 27001 access control policy template. An access and permission policy is another key component of information security in any organization. An access and permission policy is another key component of information security in any organization. A cyber security policy template can simplify the process of policy creation. Here are the critical sections your template should include. Developing a robust information security policy template requires careful attention to several key components. Sans has developed a set of information security policy templates. These are free to use and fully customizable to your company's it security practices. This course provides essential guidance to individuals with information security implementation and operational responsibilities for developing and disseminating an. Our experienced professionals will help you to customize these free it security policy template options and make them correct for your specific business needs. Below are the essential elements your policy template should include: The policy templates are provided courtesy of the state of new york and the state of california. Developing a robust information security policy template requires careful attention to several key components. This course provides essential guidance to individuals with information security implementation and operational responsibilities for developing and disseminating an. Standards a standard is set of prescribed practices or. Our list includes policy templates. Iso 27001 access control policy template. A cyber security policy template can simplify the process of policy creation. The policy templates are provided courtesy of the state of new york and the state of california. Sans has developed a set of information security policy templates. An access and permission policy is another key component of information security in any organization. Iso 27001 is part of the. An access and permission policy is another key component of information security in any organization. Establish clear responsibilities for everyone involved in managing and protecting information, from the. These are free to use and fully customizable to your company's it security practices. This policy establishes rules and procedures to control who has access to. Templates provide a structured format. Here are the critical sections your template should include. Key elements of a cyber security policy. Learn how to create a secure cloud security policy. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. Bcategories, and applicable sans policy templates. Our list includes policy templates. An access control policy defines how your organization manages user access to systems, data, and applications. The templates can be customized and used as an outline of an organizational policy, with. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. The policy. This includes systems that are managed or hosted. Consider using a cyber security policy template. Establish clear responsibilities for everyone involved in managing and protecting information, from the. Use file > download to download a copy of any of the following documents to your computer. A cyber security policy template can simplify the process of policy creation. This course provides essential guidance to individuals with information security implementation and operational responsibilities for developing and disseminating an. A cyber security policy template can simplify the process of policy creation. Our list includes policy templates. The templates can be customized and used as an outline of an organizational policy, with. Ensure compliance with applicable information security requirements. Bcategories, and applicable sans policy templates. This information security policy template applies to all systems, both automated and manual, over which the entity has administrative control. Ensure compliance with applicable information security requirements. These policy templates align with cis controls v8 and v8.1, enabling. A cyber security policy template can simplify the process of policy creation. Our list includes policy templates. Templates provide a structured format. An access control policy defines how your organization manages user access to systems, data, and applications. Formulate, review and recommend information security policies. An access and permission policy is another key component of information security in any organization. This includes systems that are managed or hosted. These policy templates align with cis controls v8 and v8.1, enabling. Establish clear responsibilities for everyone involved in managing and protecting information, from the. Learn how to create a secure cloud security policy. Bcategories, and applicable sans policy templates. Regularly assessing the information security. Implementing a comprehensive information security management system (isms) compliant with iso/iec 27001:2023 standards. Here are the critical sections your template should include. Establish clear responsibilities for everyone involved in managing and protecting information, from the. The templates can be customized and used as an outline of an organizational policy, with. For a cyber security policy to be truly effective, it should cover the following essential areas: These are free to use and fully customizable to your company's it security practices. This policy establishes rules and procedures to control who has access to. The following is a library of free information security policy templates that map to the hitrust common security framework, which in turn maps to a multitude of security frameworks (nist,. Iso 27001 access control policy template. Use file > download to download a copy of any of the following documents to your computer. An access and permission policy is another key component of information security in any organization. Templates provide a structured format. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. An access control policy defines how your organization manages user access to systems, data, and applications. This guide gives the correlation between 35 of the nist csf s.42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
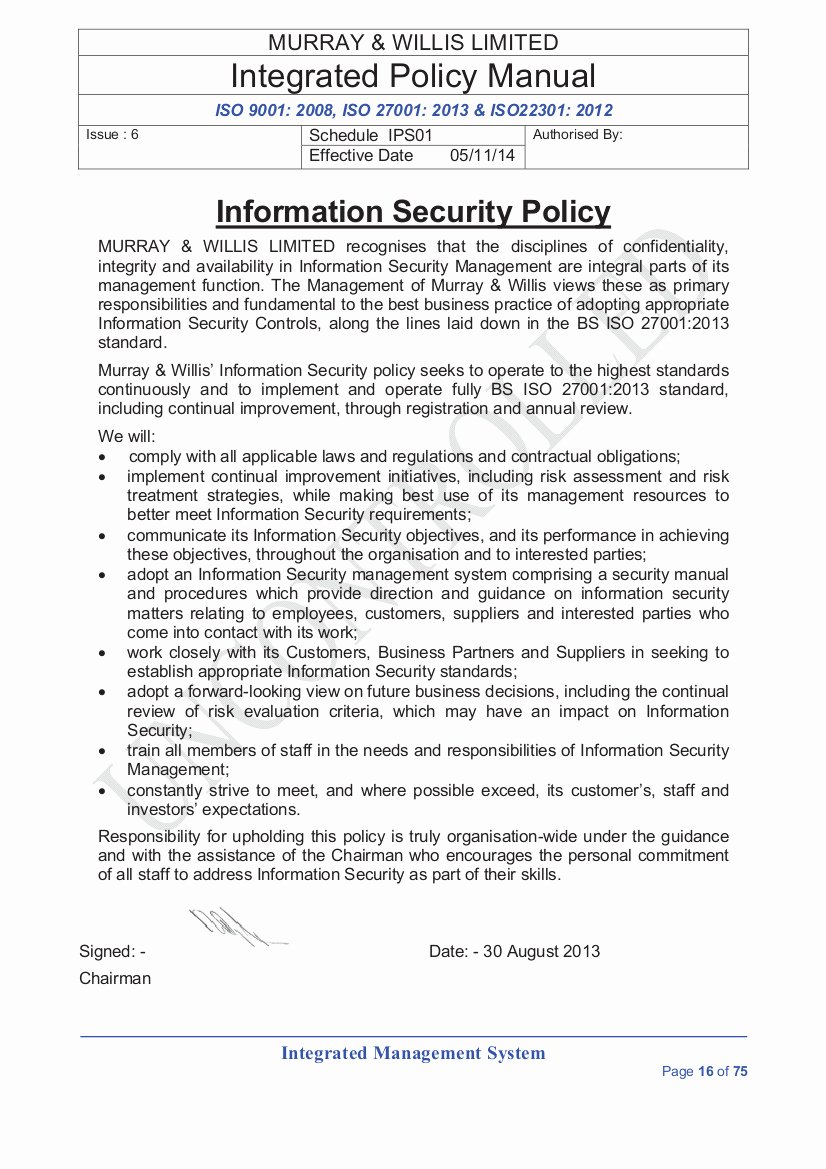
Security Policy Template 13 Free Word, PDF Document Downloads
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
Information Security Policy Template For Small Business by
Information Security Policy Template in Word, PDF, Google Docs
40 Information Security Policies Templates Desalas Template
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
This Course Provides Essential Guidance To Individuals With Information Security Implementation And Operational Responsibilities For Developing And Disseminating An.
Standards A Standard Is Set Of Prescribed Practices Or.
This Includes Systems That Are Managed Or Hosted.
Key Elements Of A Cyber Security Policy.
Related Post:
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-06.jpg)
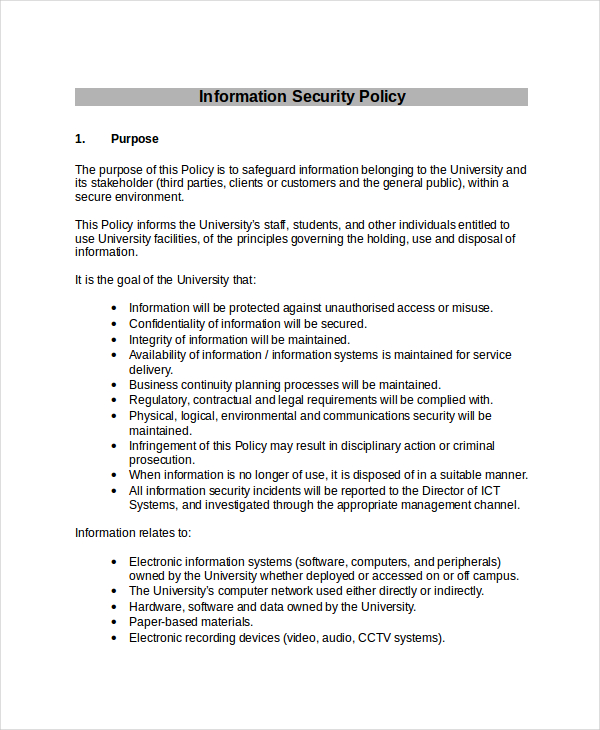
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-07.jpg?w=790)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-12.jpg)

![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-17.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-08.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-10.jpg)