Vulnerability Report Template
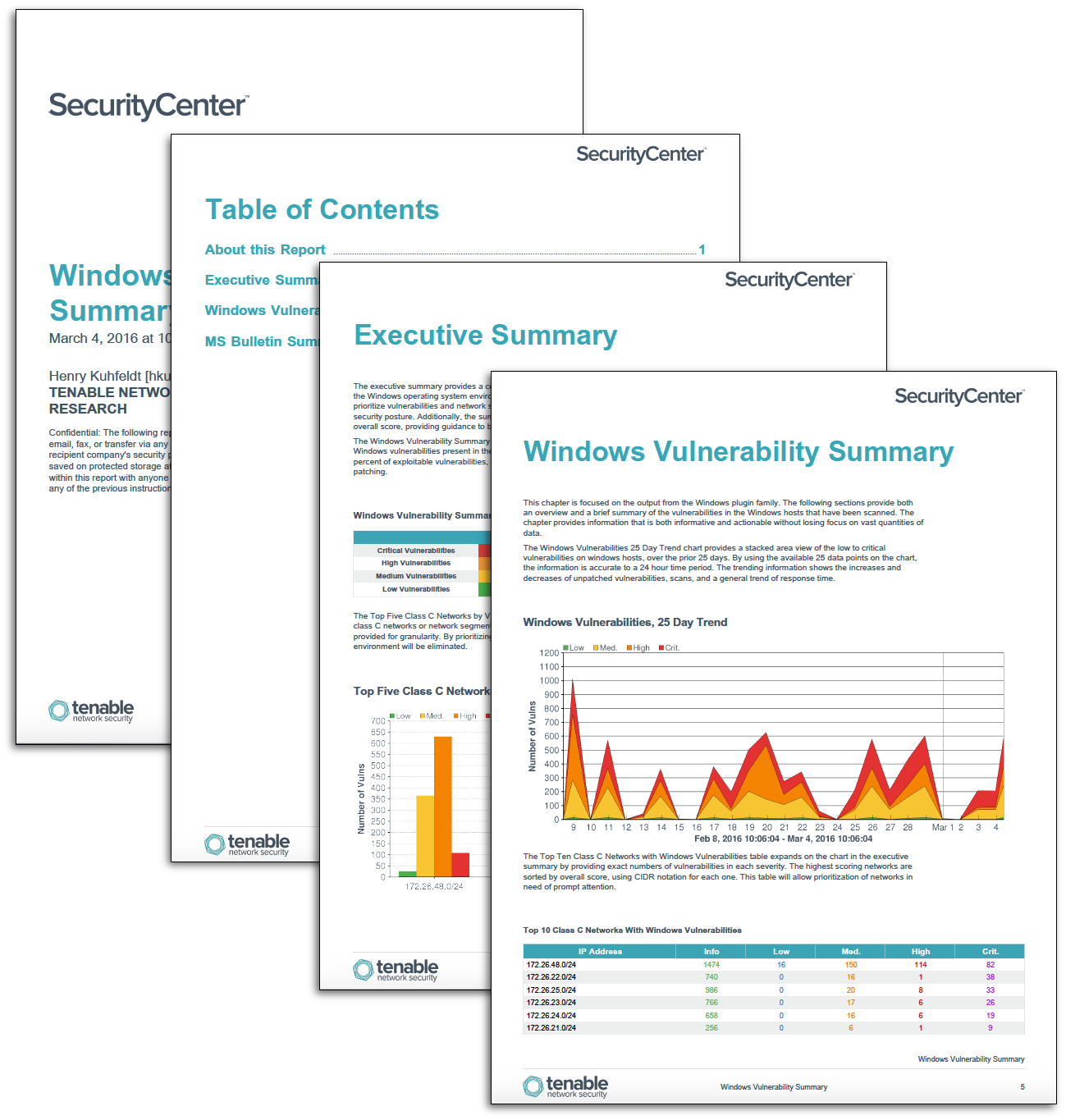
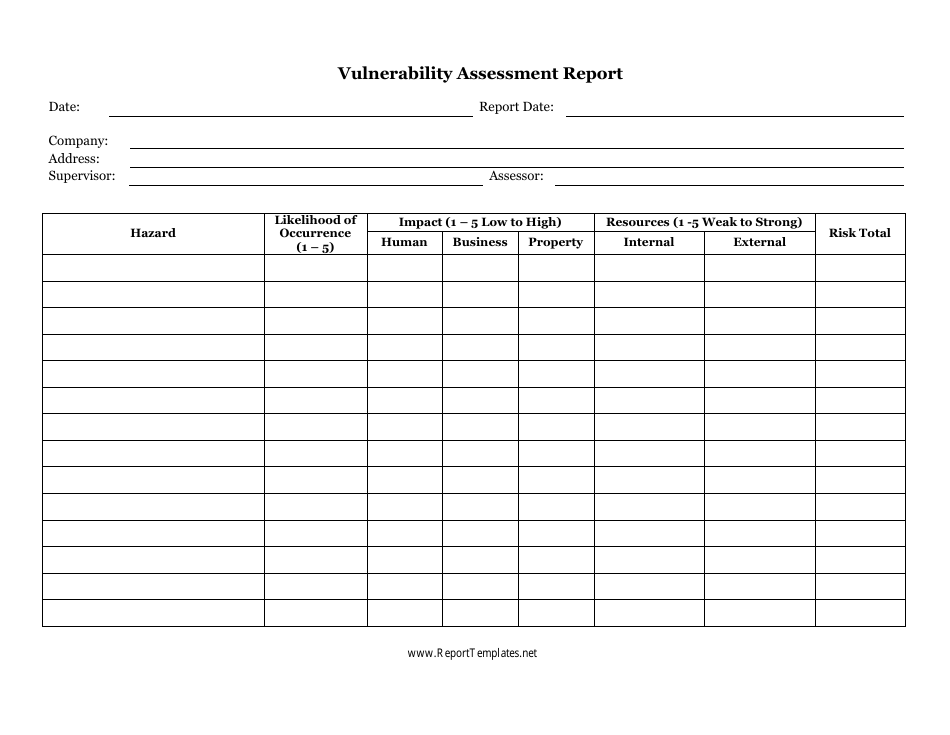
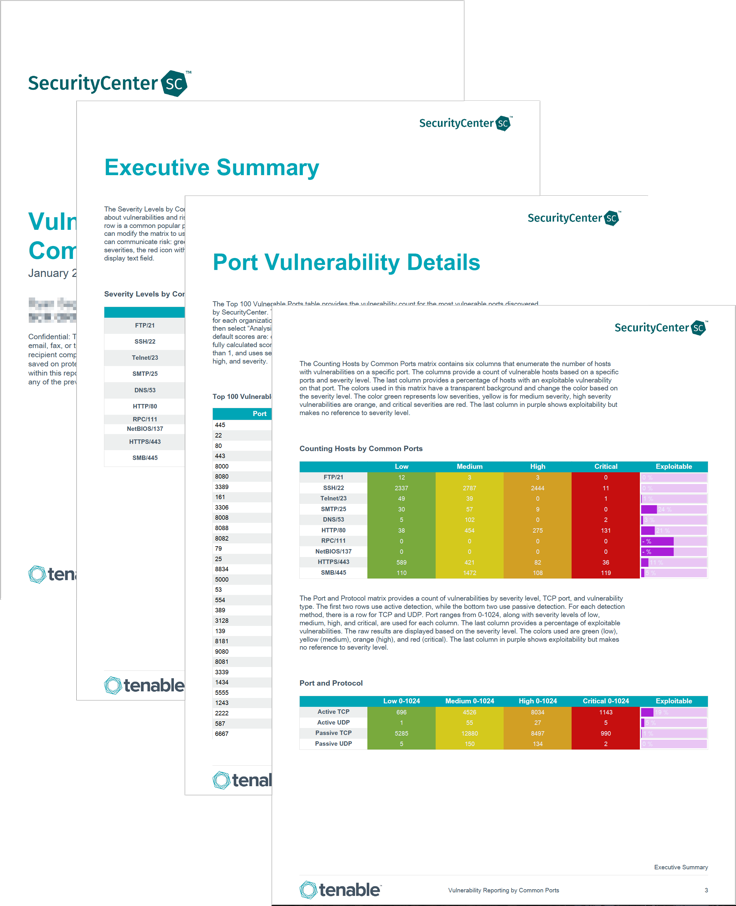
Vulnerability Report Template - The detailed findings section provides a descriptive analysis of vulnerabilities found during the security control assessment. Rate the likelihood of a hazard and its impact on a business with this vulnerability report. Critical, high, and medium severity vulnerabilities were found to exist across all 32 systems. The report assesses vulnerabilities of a database server valuable to business operations over 3 months. Application security vulnerability explanation risk recommendation It describes the server, assesses risks from threats like data exfiltration, and provides. Create own templates or use default. Free to download and print Tenable vulnerability management provides a selection of report templates and customizable report formats. Vulnrξpo is a free open source project designed to speed up the creation of it security vulnerability reports and can be used as a security reports repository. Free to download and print Application security vulnerability explanation risk recommendation Vulnrξpo is a free open source project designed to speed up the creation of it security vulnerability reports and can be used as a security reports repository. Rate the likelihood of a hazard and its impact on a business with this vulnerability report. The detailed findings section provides a descriptive analysis of vulnerabilities found during the security control assessment. Import cve, cwe, mitre att&ck or pci dss. Create own templates or use default. Identify and mitigate security risks with our vulnerability assessment report templates, designed to analyze threats, assess weaknesses, and enhance cybersecurity. Creating a vulnerability assessment report involves analyzing an organization’s systems, diagnosing system vulnerabilities, and describing the severity of those vulnerabilities. Bug bounty report writing requires special attention to detail and a structured approach to effectively communicate security findings to organizations. The report assesses vulnerabilities of a database server valuable to business operations over 3 months. Application security vulnerability explanation risk recommendation Tenable vulnerability management provides a selection of report templates and customizable report formats. Vulnrξpo is a free open source project designed to speed up the creation of it security vulnerability reports and can be used as a security reports. Bug bounty report writing requires special attention to detail and a structured approach to effectively communicate security findings to organizations. Templates of issues, cwe,cve,mitre att&ck,pci dss, import. Application security vulnerability explanation risk recommendation Creating a vulnerability assessment report involves analyzing an organization’s systems, diagnosing system vulnerabilities, and describing the severity of those vulnerabilities. Import cve, cwe, mitre att&ck or pci. Templates of issues, cwe,cve,mitre att&ck,pci dss, import. Tenable vulnerability management provides a selection of report templates and customizable report formats. Import cve, cwe, mitre att&ck or pci dss. This document provides a template for a security assessment. The report assesses vulnerabilities of a database server valuable to business operations over 3 months. Create own templates or use default. This document provides a template for a security assessment. Creating a vulnerability assessment report involves analyzing an organization’s systems, diagnosing system vulnerabilities, and describing the severity of those vulnerabilities. Bug bounty report writing requires special attention to detail and a structured approach to effectively communicate security findings to organizations. Rate the likelihood of a. This document provides a template for a security assessment. Identify and mitigate security risks with our vulnerability assessment report templates, designed to analyze threats, assess weaknesses, and enhance cybersecurity. Create own templates or use default. Application security vulnerability explanation risk recommendation The report assesses vulnerabilities of a database server valuable to business operations over 3 months. Rate the likelihood of a hazard and its impact on a business with this vulnerability report. Import cve, cwe, mitre att&ck or pci dss. Bug bounty report writing requires special attention to detail and a structured approach to effectively communicate security findings to organizations. This document provides a template for a security assessment. Vulnrξpo is a free open source project. Vulnrξpo is a free open source project designed to speed up the creation of it security vulnerability reports and can be used as a security reports repository. Free to download and print The use of templates greatly speeds up the work for pentester or security auditor. Create own templates or use default. Import cve, cwe, mitre att&ck or pci dss. Import cve, cwe, mitre att&ck or pci dss. Create own templates or use default. The detailed findings section provides a descriptive analysis of vulnerabilities found during the security control assessment. The use of templates greatly speeds up the work for pentester or security auditor. It describes the server, assesses risks from threats like data exfiltration, and provides. Create own templates or use default. The detailed findings section provides a descriptive analysis of vulnerabilities found during the security control assessment. Tenable vulnerability management provides a selection of report templates and customizable report formats. This document provides a template for a security assessment. Critical, high, and medium severity vulnerabilities were found to exist across all 32 systems. Templates of issues, cwe,cve,mitre att&ck,pci dss, import. Vulnrξpo is a free open source project designed to speed up the creation of it security vulnerability reports and can be used as a security reports repository. The use of templates greatly speeds up the work for pentester or security auditor. Create own templates or use default. The detailed findings section provides a. The use of templates greatly speeds up the work for pentester or security auditor. The report assesses vulnerabilities of a database server valuable to business operations over 3 months. Rate the likelihood of a hazard and its impact on a business with this vulnerability report. Creating a vulnerability assessment report involves analyzing an organization’s systems, diagnosing system vulnerabilities, and describing the severity of those vulnerabilities. Critical, high, and medium severity vulnerabilities were found to exist across all 32 systems. Vulnrξpo is a free open source project designed to speed up the creation of it security vulnerability reports and can be used as a security reports repository. Tenable vulnerability management provides a selection of report templates and customizable report formats. This document provides a template for a security assessment. Free to download and print Templates of issues, cwe,cve,mitre att&ck,pci dss, import. It describes the server, assesses risks from threats like data exfiltration, and provides. Create own templates or use default. Identify and mitigate security risks with our vulnerability assessment report templates, designed to analyze threats, assess weaknesses, and enhance cybersecurity.14+ Vulnerability Assessment Templates PDF, DOC, Pages
Onsite or Remote Vulnerability Assessment Services
Vulnerability Report Template
Free Sample Vulnerability Assessment Report PurpleSec
Vulnerability Assessment Report Template Fill Out, Sign Online and
Vulnerability Reporting Template
Vulnerability Report Template
Vulnerability Assessment Template Download Printable PDF Templateroller
Vulnerability Management Report Template
Vulnerability Scan Report Template
Import Cve, Cwe, Mitre Att&Ck Or Pci Dss.
Bug Bounty Report Writing Requires Special Attention To Detail And A Structured Approach To Effectively Communicate Security Findings To Organizations.
The Detailed Findings Section Provides A Descriptive Analysis Of Vulnerabilities Found During The Security Control Assessment.
Application Security Vulnerability Explanation Risk Recommendation
Related Post: